Dr. Qing Hui Awarded DOD DTRA Grant to Developing a New Approach to Network Systems in Defense Against WMDs
By Amanda Miller
The threat of possible weapons of mass destruction (WMD) attacks on U.S. soil has grown significantly within the past several years. Increasing levels of electronic interconnectivity coupled with advanced technology and political unrest has rendered the possibility of a WMD attack no longer inconceivable. If a WMD attack were to breach our defenses, the significant loss of human life, damage to our economy, and destruction of the nation's infrastructure would be unbearable if not incomprehensible. Even the mass destruction of one to two square miles of a highly populated city such as New York or Los Angeles could result in hundreds of thousands of lives lost. On the other hand, comparatively smaller attacks could result in the power loss and transportation shutdown of an entire urban area. For these reasons, the defense mechanisms in place to counter WMD attacks have recently become a main focus for the Department of Defense (DOD) and the Defense Threat Reduction Agency (DTRA).
One important tool utilized in threat reduction is advanced networked control technology. It is possible to utilize ground devices with mobile sensors to detect threats and provide information regarding the threat's whereabouts crucial to the decision-making process in event of a WMD attack. However, current methods have many limitations that must be eliminated if defense against WMD attacks is to be successful. It has been traditionally common in control theory to focus on a single controller for a single system, a very static and linear approach. For example, one device or sensor is monitoring for explosives, while another device is searching for something else, with little to no interaction or communication between the two. However, this ideology is difficult to apply to a scenario in which there are multiple controllers of an entire network (the way these mobile sensors should be). It would be more beneficial to have several devices interacting with each other and adapting to new situations, searching for multiple objects, and responding accordingly when one or more of them is found. Also, in the past, it would be possible for a WMD threat to cause complete failure to a multi-agent network due to the fact that the malfunction of one part of the network leads to a catastrophic collapse of the network as a whole. This means that any one "weak link" or localized failure could lead to the destruction of the entire network, in this case, potentially the telecommunication and infrastructure of an entire city. Lastly, existing literature regarding the mobile search for WMD threats include simple assumptions and limited search capabilities. For example, one device can search for one object, ending its search once its single goal is achieved. For this technology to be as useful and dynamic an approach as our nation's defense requires, a new model is needed.
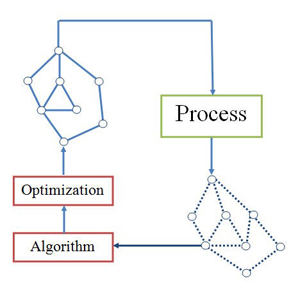
In response to this, Dr. Qing Hui, associate professor of mechanical engineering at Texas Tech University, is developing a novel approach to damage mitigation and resource allocation in network systems particularly for defense against WMDs. This approach will be developed through a balanced coordinated algorithm, in which the actions taken for damage mitigation and resource allocation will be developed within peer-to-peer networks and damage compensation is proportional to the severity of the threat or damage caused by an attack. In other words, individual agents in the network will be able to interact with each other and adapt to new situations more effectively. This design framework will be more robust and serves as a means to enhance the self-healing of a network as well as dissemination of network resources, so that responses to network damages and threats by WMDs will be optimal.
Hui is, first, proposing a new model for physical networks that will – unlike ever before possible – capture the complicated dynamics of multi-agent networks and will be more accurate than previous static connection models. Hui will develop a mathematical and computational framework that will detect both the severity and the location of WMD threats. Second, Hui will develop measures to address optimal defense strategies for decision-making. This part of the research will involve allowing for fast decision-making, finding the weakest links of a network under attack, and appropriately allocating resources and mitigating damage of those areas. In addition, Hui's semistability control theory, which addresses the stability and reliability of controls even under WMD attacks, will be applied during the algorithm design of the entire project.
Hui is in collaboration with Dr. Philip Smith from the High Performance Computing Center at Texas Tech University on this project. A total of five outstanding graduate students have been or will be a part of this research. In addition, a new senior level undergraduate course titled Industrial and Networked Control Systems will be available soon for students to study the findings of this research as well as other industrial or defense applications of network control. Hui also hopes to in the future offer a special seminar course that will focus even more closely on the findings and methods of this research. Hui explains that the ultimate goal of this research is to provide DTRA with a technology transfer that will include a new software package allowing greater damage mitigation and resource allocation capabilities in the case of a WMD threat. These novel algorithms will make it possible to analyze WMD scenarios, locate the source of the threat, and respond swiftly and effectively in response to a threat based on its severity. With Hui's novel approach, it will be possible to enhance and optimize our defense against WMD attacks, and to protect critical infrastructure such as power grids and transportation systems from such threats in the future.
Grant Title:
Balanced Coordinated Algorithms for Damage Mitigation and Resource Allocation in Network Systems
Edward E. Whitacre Jr. College of Engineering
-
Address
100 Engineering Center Box 43103 Lubbock, Texas 79409-3103 -
Phone
806.742.3451 -
Email
webmaster.coe@ttu.edu
