Researchers Recognized for Rapid COVID-19 Test, Defensive Phone Charger
By: Kaitlyn Hale
Two Texas Tech researchers were named Defense Innovation Awardees at the Defense TechConnect Summit & Expo, a summit that connects leading industry, government, and academic leaders with today's top innovators.
The awardees are selected by a panel of independent judges based on the potential positive impact a product could have. They represent the top 15 percent of more than 500 inventions at the summit.
Texas Tech researchers were recognized for a portable, rapid COVID-19 test, and a phone charger that protects power usage data from being collected from public charging stations.
"It's a big deal for this technology in terms of finding the right industry partners, talking to the right funding agencies from the government to get grant funding," said Hutton Jones, a licensing associate in Texas Tech's Office of Research Commercialization. "When they see that this is an innovation award winner, that carries some weight."
Rapid COVID-19 Testing
Gerardine Botte is a professor and Whitacre Department Chair in the Whitacre College of Engineering. She led a team including doctoral student Ashwin Ramanujam and Sharilyn Almodovar, an assistant professor in the School of Medicine at Texas Tech University Health Sciences Center, to create a rapid COVID-19 test that is as accurate as the gold standard for current testing and faster than present rapid tests.
Polymerase chain reaction (PCR) COVID-19 tests are the most accurate COVID-19 test available, but they often require sending the samples to a laboratory and waiting, sometimes days, for the results. Even current rapid tests can take up to half an hour for results, and a person with a negative result could still have COVID-19.
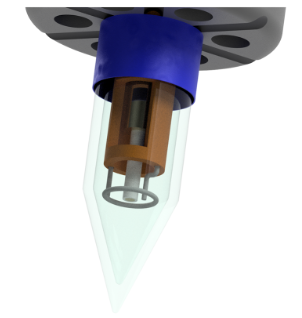
Botte's test is small enough to be hooked to a smart phone, requires only a drop of saliva, and delivers results in a matter of seconds. Botte said laboratory tests have demonstrated that her technology has the same accuracy as the PCR test.
Botte is founder and chief technology officer of a new startup working to take the product to the marketplace. The company recently received a grant from the Texas Tech Innovation Hub at Research Park to create a protype of the product.
Two forms of more stringent testing will also begin soon: with COVID-19 patients at TTUHSC and in the laboratory using 200 random samples from Texas Tech Institute of Environmental and Human Health's Biological Threat Research Laboratory.
Botte said the rapid test could help researchers collect more data more often than the current testing model allows. Given the ultra-fast response and portability, it can also be adapted to monitor air and water resources.
"It can tell me not only if I have it or not, but how are the concentration levels in my saliva? It gives you more information than we have right now," Botte said. "What happens if a person plays a sport? That's a question I have. Does the person get rid of the virus faster because he's an athlete?"
Being able to test a person multiple times a day can help answer that question and others like it, while also making testing more widely accessible.
Botte said she recognizes the value of TechConnect because of its unique opportunity to provide access to collaborators and partnerships as well as investors, federal funding agencies and industry leaders all at once.
The innovation award's judging panel includes entrepreneurs and members of industry who determine which innovations they think will have a high degree success in the marketplace.
"That's the meaning of this award for me," Botte said. "It's a revalidation that a panel is recognizing this as an innovative technology. That means that we have an opportunity with this."
Defensive Charging

Charging a phone in a public place like a café or an airport doesn't seem like any more of a risk to personal security than it would be plugging it into a wall at home, but as public charging hubs become more popular, so do efforts to exploit them.
By embedding power meters into a charging station, attackers can leverage patterns in a phone's power draw to make inferences about a user's activities on the phone. This type of attack, called a power side-channel attack, could enable the attacker to determine a wide range of typically private attributes, such as websites visited by the victim, text typed on the phone like PINs or passwords, or content consumed like songs in a playlist. An attacker could also determine activities like the usage of the camera and occurrence of incoming calls.
Researchers have created a phone charger that morphs the current drawn by the phone, camouflaging the unique patterns of a user's activities from these types of attacks. As an alternative to the charger, they have also built a software-based form of the solution which automatically kicks in during charging. Abdul Serwadda, an assistant professor in the Department of Computer Science and his research team and collaborators, Richard Matovu, who has since graduated with a Ph.D. in computer science, Argenis V.Bilbao, and Isaac Griswold-Steiner worked on the project.
Serwadda and his team call protecting a phone in this way defensive charging. He said this extra layer protection would only add a couple of dollars to the cost of a conventional phone charger and would have no effect on the actual CPU and memory usage of the phone.
"We augment the traditional charging pipeline with mechanisms in your smartphone charger that make sure that if someone tampered with that charging hub at the airport or other public place, they'll never get the correct power patterns," Serwadda said. "It kind of masks your footprint, so you don't have to move around so worried about whether you can trust that random charging hub. As long as you have our solution, you're safe from that type of attack."
Though the product is only in the prototyping stages, it's relevant in a time when people are increasingly dependent on their phones. The fact that a power side-channel attack does not require the adversary to install some sort of malware on the victim's phone makes it very easy to exploit by malicious actors.
"Defense contractors, military personnel, sensitive government personnel at this defense conference, this is something they are becoming more and more aware of," Jones said. "They're always going to have to plug into an airport power jack or at a hotel. It's an emerging threat, so we're kind of out front on that one."
This isn't the first time this new charging paradigm innovation has been recognized. In March, Serwadda and his research team were published in the 2020 Association for Computing Machinery Conference on Data and Application Security and Privacy, a conference that accepts less than 20 percent of submissions each year.
However, Serwadda said the Defense TechConnect Innovation Award confirms his team was right that this research is fundamental.
"This conference is one of the signs that makes everyone realize the importance of this," he said.
Discoveries
-
Address
Texas Tech University, 2500 Broadway, Box 41075 Lubbock, TX 79409 -
Phone
806.742.3905 -
Email
vpr.communications@ttu.edu
